Welcome to the Axiomise Blog
At Axiomise, we’re passionate about advancing the frontiers of formal verification. Our Tech Blog is where innovation meets insight, a dedicated space where our engineers, researchers, and thought leaders share deep dives into formal methods, real-world verification challenges, cutting-edge tools, and lessons learned from the field.
Whether you’re an industry expert, a verification engineer, or simply curious about the power of formal, this blog is your window into the minds shaping the future of semiconductor design verification. Expect hands-on tutorials, expert commentary, project highlights, and the latest updates from the formal ecosystem.
Explore. Learn. Challenge the status quo, formally.
Technical Articles
Filter and search content by topic, category, or tag.
11 Questions about Formal Verification
DVCon USA revealed that formal verification is already handling billion-gate designs—but the real challenge is not tools, but methodology and how effectively it is applied in real-world verification flows.
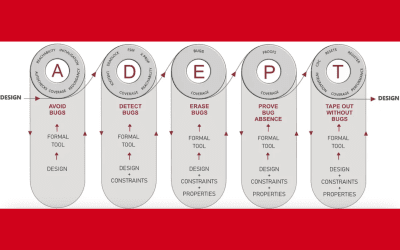
Becoming ADEPT in Formal Verification
The ADEPT FV flow applies formal verification across the entire design lifecycle—Avoid, Detect, Erase, and Prove—to catch bugs early, strengthen correctness, and build continuous coverage, enabling more robust, scalable, and predictable tape-out.
Exhaustive Formal Verification of Packet Based Designs
Serial packet-based designs are difficult to verify due to deep state dependencies and history-sensitive behavior. By using abstraction techniques such as smart tracking and assume-guarantee reasoning, verification becomes scalable while still ensuring correct packet ordering and significantly improving proof convergence.
Living life in the Formal Lane with Confidence
Despite its proven value, formal verification remains underused due to gaps in training, methodology, processes, and consistent application across projects. Making formal mainstream requires a systematic approach, the right expertise, and continuous support to deliver more reliable, bug-free designs at scale.
Ten Rules to Successfully Deploy Formal
Formal verification success is not driven by expertise alone, but by methodology and disciplined execution. Focusing on requirements, prioritising effectively, combining formal with simulation, and using strong planning, coverage, and reviews makes it a practical and high-impact verification approach.
When ” Silicon Proven” Is Not Good Enough
From Meltdown to Spectre, hidden vulnerabilities exposed deep flaws in modern computing, showing that security is not just a software concern but a fundamental hardware challenge that must be addressed at design time to prevent costly failures.
My Journey into Formal Verification Explained
From a childhood surrounded by engineering in India to influencing formal verification at companies like Intel, ARM, and OneSpin, this journey reflects curiosity, persistence, and global impact. It mirrors the evolution of an entire field and shows why formal verification is now essential in modern technology.
The Evolution of formal verification I
Human ingenuity has driven extraordinary technological advances, from early architecture to modern semiconductor systems, but verification and testing have not evolved at the same pace. This has created a critical gap in ensuring quality, safety, and security in today’s increasingly complex digital world.
The evolution of formal verification II
Formal methods in practice focus on property checking through assertion-based verification—a practical, tool-driven approach to proving design behavior with precise properties. Engineers can quickly start by writing SVA or PSL assertions that capture cause-and-effect behavior, enabling automated and exhaustive verification without manual stimulus.